Category: Technology
From Paper to Toner: Photocopier Environmental Impacts You Should Know
It’s becoming more important for companies to reduce their environmental impact. Businesses can help the environment by using eco-friendly printers and paper cartridges as well as strategies to reduce waste.
An excellent place to start is to track your copier energy consumption accurately. Installing waste sorting stations, informing your employees to use digital proofs in place of paper ones and creating waste sorting stations for ink and paper cartridges can help you reduce the carbon footprint of your office.
Energy consumption
Photocopiers are energy-intensive and can have a negative effect on the environment. Making use of eco-friendly printers and paper, as well as making sure they are properly maintained, will help lessen their impact on the environment. Also, ensuring to recycle cartridges as well as paper can significantly impact the environment.
The ozone generated by photocopiers is harmful to the health of humans since it could cause breathing issues and eye irritations. This is particularly the case for those with an illness that affects the respiratory system, such as asthma. Offices must install ventilation systems that allow fresh air into the room as well as removing dust and unpleasant odors.
Photocopiers can consume large amounts of paper. This is not only not sustainable, but it could be a contributing factor to loss of forest habitat. By switching to recycled paper and using vegetable or soy-based inks as opposed to conventional inks, you can reduce your copier’s environmental impact. Training staff on how to print more efficiently by encouraging double-sided printing and using draft mode can further reduce unnecessary printing.
Photocopiers can be greatly reduced in energy consumption by choosing an Energy Star copier and making sure that the machine is shut off or put into sleep mode when it is not used. In addition, establishing an office recycling programme for cartridges of toner and paper can make a huge difference.
Wasted Photocopier Paper
The waste of paper is among the largest environmental problems. Many factors are responsible for this, such as documents that aren’t utilized, printing errors and the packaging that results from the delivery of products. This issue can be avoided with effective management of business operations as well as implementation of sustainable photocopier practices. Businesses can reduce the amount of paper they use by recycling paper. You can save energy by turning off the machine while it’s not in use or printing two-sided.
Another factor is the deforestation of natural forests in the manufacture of paper. These forests are replaced by plantation forests that do not support biodiversity. These new trees are also more susceptible to climate change and drought. The demand for paper is also increasing, which is driving deforestation. Fortunately, organizations like the Prince’s Rainforest Project are working to stop this trend, but it is important for companies to decrease the use of paper as well as other products.
Photocopiers release high levels of particulate matter, which can trigger respiratory ailments. Long-term exposure to these emissions can affect lung function as well as increase the inflammatory process and oxidative stress. This can lead to poor work performance headaches, fatigue, and an increase in immune function. It is therefore important to avoid exposure to chemicals.
Toner cartridge environmental impact
Cartridges that are disposed of irresponsibly can release harmful pollutants into the environment, polluting water and air. The chemicals also can affect the quality of air in the home and impact the health of individuals. Every second 11 ink and toner cartridges in the US are discarded in a way that is not properly and create a lot of waste.
Recycled cartridges are an important way to reduce the impact on the environment of the photocopier. It can help reduce the requirement for new cartridges and also the carbon emissions generated during the extraction of the raw material.
In addition, it’s essential to inform employees about sustainable practices, such as two-sided printing, and using draft mode even when a quality copy isn’t required. This will help reduce printing and paper waste.
Numerous printer makers and other third-party companies offer recycling programs for cartridges, which allow workplaces to return used cartridges. The cartridges are then used again, thus reducing waste and promoting material reuse.
Find photocopiers that are ENERGY EPEAT or STAR certified when selecting one for your business. These certifications can help cut down on the use of energy, air pollution as well as carbon emissions as well as reducing the operational expenses. In addition, consider the sustainability record of the vendor and their commitment to a circular economy. Find a supplier that provides recycling, returns and reuses programs, in addition to proactive and remote equipment maintenance services.
Photocopier E-waste
As the world transitions to digital record-keeping, old Thue may photocopy Binh Duong copiers and other equipment that were once a necessity is being removed. Most people are unaware that disposing of older equipment such as printers or photocopiers can have a negative impact on the environmental.
E-waste, which is also known as waste of electronic and electrical equipment is one of the world’s fastest-growing waste streams. It is a great source for hazardous waste and needs special care. E-waste contains several toxic components that could emit harmful chemicals to the environment.
The toxic substance is harmful to the environment as well as human health. Inadequately treated e-waste could result in soil pollution, water pollution and air pollution. It could also pose a danger to workers who participate in the process of processing the e-waste, including pregnant women and children.
Because of their capacity to cross placentas and contaminate the milk supply, nursing and pregnant mothers face an increased chance of being exposed to eWaste-related contaminants. E-waste exposure can negatively impact the development of the body and brain of infants.
In order to reduce e-waste, governments should provide incentives to companies that help them develop sustainable products. They should also encourage responsible recycling practices. These incentives could include tax credits or procurement policies. They can also give guidelines to decrease the amount of hazardous materials in electronics.
Innovative Battery Equivalents to Transform with Efficiency and Longevity Replacements
Battery technology has been evolving at an impressive pace, driven by the demand for more efficient, sustainable and longer-lasting energy storage solutions. Traditional batteries, such as those found in smartphones, electric vehicles, and renewable energy systems, have had their limitations. However, recent innovations in battery equivalents are transforming the landscape with improved efficiency and longevity. These new battery solutions not only enhance performance but also address critical issues like environmental sustainability, energy density, and cost-effectiveness. Let’s explore how innovative battery equivalents are shaping the future of energy storage.
Next-Generation Materials
One of the primary drivers of advancements in battery technology is the use of next-generation materials. Traditional lithium-ion batteries, while still widely used, are being replaced or supplemented by alternatives that offer superior performance. For instance, solid-state batteries use a solid electrolyte instead of a liquid one, which improves energy density and reduces the risk of leaks or fires. Additionally, materials like silicon and graphene are being integrated into battery design. Silicon, for example, can store significantly more lithium ions than graphite, leading to longer battery life. Similarly, graphene enhances conductivity and allows for faster charging.
Enhanced Energy Efficiency
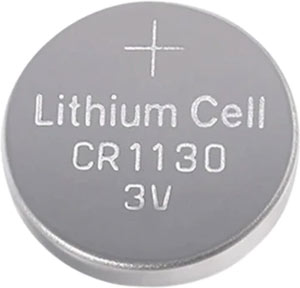 The efficiency of battery equivalents is a key factor that determines their viability in various applications. New technologies are focusing on reducing energy losses during charging and discharging processes, making batteries more efficient. For example, lithium-sulfur Li-S batteries offer a higher energy-to-weight ratio than traditional lithium-ion batteries. This makes them ideal for applications like electric vehicles EVs and aerospace, where weight and energy density are crucial. Additionally, advancements in nanotechnology allow for better control of chemical reactions within the battery, minimizing waste and maximizing output.
The efficiency of battery equivalents is a key factor that determines their viability in various applications. New technologies are focusing on reducing energy losses during charging and discharging processes, making batteries more efficient. For example, lithium-sulfur Li-S batteries offer a higher energy-to-weight ratio than traditional lithium-ion batteries. This makes them ideal for applications like electric vehicles EVs and aerospace, where weight and energy density are crucial. Additionally, advancements in nanotechnology allow for better control of chemical reactions within the battery, minimizing waste and maximizing output.
Extended Longevity
One of the most significant innovations in modern AG13 battery equivalent has the extension of their lifespan. Traditional batteries degrade over time due to repeated charge and discharge cycles, leading to reduced capacity and eventually failure. However, new battery chemistries and designs are addressing this issue by improving durability and stability. Solid-state batteries, for example, are less prone to degradation than liquid-based batteries, which help extend their useful life. Researchers are also exploring the potential of using advanced coatings and self-repairing materials that can further enhance battery longevity, reducing the need for frequent replacements.
Environmental Sustainability
As the world shifts towards renewable energy sources, the environmental impact of batteries has become a critical concern. Traditional battery manufacturing processes often rely on rare and toxic materials like cobalt, which are both environmentally harmful and ethically problematic due to mining practices. New battery equivalents are focusing on sustainability by using more abundant and less harmful materials. For instance, sodium-ion batteries are gaining attention as a potential replacement for lithium-ion batteries because sodium is more readily available and less harmful to extract. Additionally, advancements in recycling technology are enabling the recovery and reuse of battery components, reducing waste and conserving resources.
AI and Excel – A New Era of Intelligent Spreadsheets for Data-Driven Businesses
The integration of Artificial Intelligence AI into Microsoft Excel signifies a transformative leap into a new era of intelligent spreadsheets, reshaping the landscape for data-driven businesses. Excel, a longstanding stalwart in the world of data management, is now enhanced by AI technologies that infuse it with advanced capabilities previously unimaginable. This evolution is driven by the need for businesses to process, analyze, and interpret vast amounts of data efficiently and effectively, making AI an invaluable tool in this endeavor. AI’s impact on Excel manifests in several groundbreaking ways. One of the most notable advancements is the introduction of automated data analysis and predictive modeling features. These capabilities leverage machine learning algorithms to identify patterns, trends, and anomalies in data, providing users with insights that would have otherwise required extensive manual analysis. For instance, AI-powered tools can automatically generate complex formulas and functions, reducing the need for users to have an in-depth understanding of Excel’s more intricate features. This not only speeds up the analysis process but also democratizes access to advanced data insights, allowing users at all skill levels to leverage sophisticated data techniques.
Another significant advancement is the development of natural language processing NLP within Excel. This allows users to interact with their spreadsheets in a more intuitive manner, using everyday language to query data. Users can simply type questions like what were the sales figures for Q1. Or Show me trends in customer acquisition over the past year, and Excel will interpret these queries, providing relevant data and visualizations. This feature lowers the barrier to effective data analysis, making it accessible to those who may not be well-versed in data manipulation or programming. AI also enhances Excel’s data visualization capabilities. Traditional charts and graphs are now complemented by intelligent recommendations that suggest the most appropriate visualizations for the data being analyzed. These excel formula generator suggestions help users create more insightful and impactful visual representations of their data, facilitating better decision-making. Additionally, AI tools within Excel can automatically generate summaries and reports, highlighting key findings and trends, which streamlines the process of reporting and presentation.
Moreover, AI integration in Excel supports advanced data cleaning and preparation tasks. Data often comes with inconsistencies, errors, or formatting issues that need to be addressed before meaningful analysis can occur. AI algorithms can automatically identify and correct these issues, significantly reducing the time and effort required for data preparation. This ensures that users spend more time analyzing and interpreting their data, rather than getting bogged down by data wrangling tasks. In summary, the infusion of AI into Excel marks a pivotal shift towards more intelligent, efficient, and user-friendly data management solutions. For businesses that rely on data-driven decision-making, these advancements are not just enhancements but essential tools that drive productivity and insights. By harnessing the power of AI, Excel is evolving from a traditional spreadsheet application into a sophisticated platform capable of handling complex data challenges, ultimately empowering users to make more informed and strategic business decisions.
The Increasing Importance of Cybersecurity in the Digital Age
In today’s rapidly evolving digital landscape, cybersecurity has emerged as a critical component for protecting sensitive information and maintaining the integrity of digital systems. As businesses, governments, and individuals continue to embrace the benefits of digital technologies, the risks associated with cyber threats have become more pronounced. Cybersecurity encompasses a range of practices, technologies, and processes designed to safeguard computers, networks, and data from unauthorized access, theft, and damage. The growing frequency and sophistication of cyberattacks underscore the urgent need for robust cybersecurity measures to protect against a wide array of threats, including data breaches, ransomware attacks, and identity theft. One of the primary drivers behind the heightened focus on cybersecurity is the increasing reliance on digital infrastructure across all sectors. The COVID-19 pandemic accelerated the adoption of remote work, online services, and digital communication platforms, exposing vulnerabilities in existing cybersecurity frameworks. Cybercriminals have exploited these weaknesses, leading to a surge in cyberattacks targeting both individuals and organizations.
High-profile incidents, such as the SolarWinds hack and the Colonial Pipeline ransomware attack, have highlighted the potential for cyber threats to disrupt critical infrastructure and cause widespread damage. These events have underscored the need for proactive cybersecurity measures and increased investment in cyber defense capabilities. The financial implications of cyberattacks are staggering, with global losses estimated to reach trillions of dollars annually. Stay Safe and Secure online Businesses face significant costs associated with data breaches, including legal fees, regulatory fines, and reputational damage. Moreover, the loss of intellectual property and sensitive customer information can have long-lasting consequences for a company’s competitive advantage and trustworthiness. As a result, organizations are prioritizing cybersecurity as a fundamental aspect of their risk management strategies. This shift is driving demand for skilled cybersecurity professionals and advanced security technologies, such as artificial intelligence and machine learning, which can detect and respond to threats in real-time. Governments around the world are also recognizing the importance of cybersecurity and implementing policies to enhance national cyber defenses.
These regulations aim to ensure that organizations adhere to best practices in safeguarding sensitive information and mitigating cyber risks. Additionally, international cooperation is becoming increasingly important in addressing the global nature of cyber threats. As the Internet of Things IoT, 5G networks, and cloud computing continue to expand, they introduce new vulnerabilities that cybercriminals can exploit. Consequently, cybersecurity strategies must adapt to address these emerging challenges. Continuous innovation and investment in cybersecurity research are essential to stay ahead of cyber threats and protect digital assets. In conclusion, cybersecurity is a paramount concern in the digital age, requiring a comprehensive and dynamic approach to safeguard against an ever-evolving array of threats. The increasing reliance on digital technologies, coupled with the growing sophistication of cyberattacks, necessitates robust cybersecurity measures across all sectors. By prioritizing cybersecurity and fostering collaboration among stakeholders, we can build a resilient digital ecosystem that protects sensitive information and ensures the continuity of critical services.
Maximize Your Marketing Efforts – How Buying a ChatGPT Account Can Help You
In today’s digitally driven world, effective marketing is crucial for businesses aiming to stay competitive and relevant. One innovative tool that has revolutionized marketing strategies is leveraging ChatGPT accounts. These accounts are powered by advanced artificial intelligence AI and can significantly enhance your marketing efforts in several key ways.
Personalized Customer Interaction – ChatGPT accounts excel in providing personalized customer interactions. They can engage with potential customers in real-time, offering tailored responses based on individual inquiries and preferences. This personalized approach not only improves customer satisfaction but also enhances the likelihood of converting leads into loyal customers. By understanding customer needs and providing relevant information promptly, ChatGPT accounts create a positive user experience that strengthens your brand’s reputation.
24/7 Availability – Unlike human agents, ChatGPT accounts operate round-the-clock, ensuring continuous availability to address customer queries and provide support at any hour of the day. This accessibility is invaluable in today’s global marketplace, where customers expect immediate responses and assistance. By integrating a ChatGPT account into your marketing strategy, you ensure that potential leads are never left waiting, thus improving customer retention and satisfaction.

Scalability and Efficiency – Scaling customer support and marketing efforts can be challenging without incurring substantial costs. ChatGPT accounts offer a scalable solution by handling multiple customer interactions simultaneously without compromising on response quality. Whether you are dealing with a handful of inquiries or a surge in traffic, these accounts can efficiently manage workload peaks, ensuring consistent service delivery without the need for extensive human resources.
Enhanced Lead Generation and Conversion – ChatGPT accounts can actively engage website visitors and social media followers, guiding them through the sales funnel with personalized recommendations and information. Through proactive engagement, these accounts nurture leads, address objections, and facilitate conversions by providing relevant information and fostering trust. This proactive approach not only accelerates the sales process but also increases the likelihood of securing long-term customer relationships.
Brand Differentiation and Innovation – Integrating a ChatGPT account into your marketing strategy showcases your brand’s commitment to innovation and customer-centricity. By adopting cutting-edge AI technology, you differentiate your brand from competitors and position yourself as a forward-thinking industry leader. This innovative approach not only attracts tech-savvy consumers but also reinforces brand credibility and authority in your niche market.
Cost-Effective Solution – Compared to traditional customer support channels, employing ChatGPT accounts is a cost-effective solution. It reduces overhead costs associated with hiring and training customer service representatives while delivering consistent and reliable support. The initial investment in setting up and integrating ChatGPT technology is quickly offset by the efficiency gains and improved customer satisfaction metrics it enables and check here now.
Leveraging ChatGPT accounts in your marketing strategy offers a myriad of benefits, from enhancing customer interactions and boosting engagement to generating valuable insights and improving operational efficiency. By embracing AI-powered technology, businesses can stay ahead in a competitive marketplace, drive growth, and build lasting customer relationships. Investing in a ChatGPT account is not just about adopting a new tool it is about transforming your marketing approach to meet the demands of today’s digital landscape effectively.
Security System Services – Redefining Standards in Safety and Protection
In an age where safety and protection are paramount concerns, the role of security systems has become increasingly vital. From residential neighborhoods to bustling commercial hubs, the demand for reliable security solutions continues to grow. In this landscape, security system services emerges as a pioneering force, redefining standards in safety and protection with its innovative approach and unwavering commitment to excellence. At the heart of security system services’ ethos lies a dedication to understanding and addressing the unique security needs of each client. Whether it is safeguarding a family home or securing a corporate headquarters, the company employs a bespoke approach, tailoring solutions to suit specific requirements. Through comprehensive consultations and meticulous assessments, security system services ensure that every aspect of a client’s security concerns is thoroughly analyzed and addressed. One of the cornerstones of security system services’ success is its relentless pursuit of cutting-edge technology. Recognizing that the landscape of security threats is constantly evolving, the company remains at the forefront of innovation, continually integrating the latest advancements into its offerings.
From state-of-the-art surveillance systems to advanced access control mechanisms, security system services leverages technology to provide clients with robust, future-proof solutions that offer peace of mind in an uncertain world. However, technology alone is not enough to guarantee effective security. That is why the company places a premium on recruitment and training, ensuring that its team consists of skilled professionals with the expertise to handle any situation effectively. Whether it is responding to alarms, conducting patrols, or providing emergency assistance, security system services’ personnel are trained to the highest standards, instilling confidence in clients and deterring potential threats. Moreover, security system services take a proactive stance towards security, emphasizing the importance of preventive measures alongside reactive strategies. Through comprehensive risk assessments and thorough planning, the company identifies vulnerabilities and implements preemptive measures to mitigate potential risks. By staying one step ahead of threats, security system services not only minimizes the likelihood of security breaches but also provides clients with invaluable peace of mind, knowing that their assets and loved ones are well-protected.
Central to security system services’ mission is a commitment to reliability and responsiveness. In an emergency situation, every second counts, and the ability to react swiftly can mean the difference between safety and disaster. That is why the company operates a 24/7 monitoring center staffed by trained professionals who are ready to respond to any alarm or incident, day or night. With rapid response times and efficient coordination, American Freedom Security Systems and Services ensure that clients receive the assistance they need when they need it most, reinforcing trust and confidence in the company’s capabilities. Beyond its core services, security system services is dedicated to fostering long-term partnerships with its clients, built on a foundation of trust, transparency, and integrity. By prioritizing customer satisfaction and consistently delivering exceptional service, the company has earned a reputation for excellence within the industry, setting new standards for safety and protection. Through its tailored approach, advanced technology, skilled personnel, proactive strategies, and unwavering commitment to client satisfaction, the company is redefining standards in safety and protection, setting a benchmark for excellence that others strive to emulate.
Simplify, Scale, Succeed – The Triad of Business Automation Excellence
In the dynamic landscape of modern business, the mantra of Simplify, Scale, Succeed emerges as a guiding principle for achieving automation excellence. At its core, this triad embodies a strategic approach aimed at optimizing processes, amplifying growth, and fostering sustainable success. The journey begins with simplification, a deliberate effort to streamline operations by eliminating redundancies, reducing complexities, and enhancing efficiency. Through the lens of automation, this entails leveraging technology to automate repetitive tasks, standardize workflows, and minimize manual intervention. By embracing simplicity, organizations not only enhance productivity but also lay a foundation for scalability. Scalability stands as the second pillar of this triad, representing the capacity to expand and adapt in response to evolving demands. With automation as the enabler, businesses can transcend traditional constraints and unlock newfound agility. Whether accommodating rapid growth, navigating market fluctuations, or seizing emerging opportunities, scalable systems empower organizations to flexibly adjust their operations without compromising performance or stability.
From scalable infrastructure to modular software solutions, investments in scalability position business automation to capitalize on their potential and effectively navigate the complexities of a competitive landscape. Yet, true success in business automation extends beyond mere efficiency and adaptability—it hinges on the ability to achieve meaningful outcomes and sustainable growth. Hence, the final element of this triad, success, encapsulates the realization of strategic objectives and the fulfillment of long-term aspirations. While automation lays the groundwork, success requires a holistic approach that integrates technology with human expertise, fosters innovation, and cultivates a culture of continuous improvement. By aligning automation initiatives with overarching business goals, organizations can harness its transformative power to drive innovation, enhance customer experiences, and unlock new avenues of value creation. Embracing the triad of Simplify, Scale, Succeed represents a paradigm shift in the way businesses approach automation.
Rather than viewing it as a standalone solution, it becomes an integral part of a broader strategy aimed at driving efficiency, agility, and growth. Through simplification, organizations streamline their operations, laying a foundation for scalability and resilience. Scalability, in turn, empowers businesses to expand their reach, seize opportunities, and navigate challenges with confidence. However, the ultimate measure of success lies not just in the efficiency of automation but in its ability to drive meaningful outcomes and sustainable growth. In conclusion, the journey towards business automation excellence unfolds along the triad of Simplify, Scale, Succeed. By simplifying operations, scaling infrastructure, and pursuing strategic objectives, organizations can unlock the full potential of automation and position themselves for long-term success in an ever-evolving marketplace. As technology continues to advance and business landscapes evolve, embracing this triad becomes not only a competitive advantage but a prerequisite for thriving in the digital age.
Unlocking Digital Footprints The Role of Email Lookup
In today’s digital age, where information is abundant and interconnected, the concept of privacy is often elusive. Our online activities leave behind a trail of digital footprints that can reveal a lot about us – from our interests and habits to our personal and professional connections. Among the various identifiers used in the digital realm, email addresses stand out as a ubiquitous thread tying together our online presence. Email lookup, therefore, plays a significant role in unlocking these digital footprints and piecing together a clearer picture of individuals and their activities. Email lookup involves the process of tracing and analyzing email addresses to gather information about the associated individuals or entities. This technique is employed for various purposes, ranging from personal research to cybersecurity and marketing strategies. By inputting an email address into specialized tools or platforms, users can uncover a wealth of data linked to that particular identifier.
One of the primary applications of email lookup is in the realm of cybersecurity. With the proliferation of cyber threats such as phishing scams, identity theft, and online fraud, verifying the legitimacy of an email sender is crucial. Email lookup tools enable users to scrutinize the sender’s identity, domain reputation, and previous activities associated with the email address. This information empowers individuals and organizations to make informed decisions regarding the trustworthiness of incoming emails, thereby enhancing their digital security posture. Moreover, email lookup serves as a valuable tool for digital marketers and businesses engaged in customer relationship management. By analyzing email addresses gathered from various sources, Free Reverse Lookup marketers can segment their target audience more effectively, personalize marketing campaigns, and improve customer engagement. Understanding the digital footprints left by email addresses allows marketers to tailor their messaging according to the preferences and behaviors of their prospects, thereby increasing the likelihood of conversion.
Furthermore, email lookup aids in the investigation of online activities and the verification of identities. Law enforcement agencies, private investigators, and legal professionals utilize email lookup techniques to gather evidence, track down individuals, and verify the authenticity of digital communications. By tracing the digital footprints associated with email addresses, investigators can uncover connections, uncover patterns of behavior, and establish the credibility of online personas. However, the widespread use of email lookup also raises concerns regarding privacy and data protection. As individuals become increasingly aware of the extent to which their digital footprints are being tracked and analyzed, questions arise regarding the ethical implications of email lookup practices. Striking a balance between the legitimate use of email lookup for security and investigative purposes and respecting individuals’ privacy rights remains a challenge in the digital age. email lookup plays a crucial role in unlocking digital footprints and revealing valuable insights about individuals’ online activities. From enhancing cybersecurity to facilitating marketing efforts and supporting investigative procedures, email lookup has become an indispensable tool in the digital toolkit.
The Power of Dedicated Servers for High-Traffic Websites
Dedicated servers stand as the bedrock of high-traffic websites, offering unparalleled reliability, performance, and scalability. In the ever-evolving landscape of online presence, where milliseconds can make a difference, dedicated servers emerge as the prime choice for websites inundated with heavy traffic. Their inherent robustness stems from the exclusivity they offer – the entire server is dedicated solely to one client, ensuring resources are not shared or compromised. When it comes to handling high traffic, dedicated servers shine in their ability to provide consistent performance under immense pressure. Unlike shared hosting environments, where multiple websites compete for resources, dedicated servers allocate all available processing power, memory, and bandwidth to a single entity. This exclusivity translates into enhanced speed, responsiveness, and stability, crucial factors in retaining visitors and maintaining user satisfaction. Moreover, dedicated servers empower website owners with full control over server configurations and resources. This level of autonomy enables customization tailored to specific requirements, optimizing performance and security measures. From selecting hardware specifications to choosing the operating system and software stack, dedicated server hosting grants flexibility unmatched by other hosting solutions.

This control extends to security protocols, allowing stringent measures to safeguard sensitive data and mitigate potential threats, vital for high-traffic websites handling confidential information. Scalability lies at the heart of dedicated server hosting, catering to the dynamic needs of growing websites. With the ability to easily upgrade hardware components such as CPU, RAM, and storage, dedicated servers ensure seamless expansion without compromising performance. This scalability is particularly advantageous for high-traffic websites experiencing rapid growth or seasonal fluctuations in visitor traffic. Whether it is accommodating spikes in traffic during promotional events or scaling down during quieter periods, dedicated servers offer the agility needed to adapt to changing demands swiftly. Another compelling aspect of dedicated servers is their reliability and uptime guarantee. With resources exclusively allocated to a single client, the risk of performance degradation due to external factors is significantly reduced. Downtime, a dreaded scenario for any website owner, is minimized through dedicated server hosting, ensuring uninterrupted accessibility and seamless user experience.
This reliability is further bolstered by robust infrastructure and round-the-clock technical support, providing peace of mind to website owners and instilling confidence among visitors. Furthermore, dedicated servers offer enhanced security features essential for safeguarding sensitive data and maintaining regulatory compliance. With the rise of cybersecurity threats and data breaches, stringent security measures are paramount for high-traffic websites entrusted with user information. Dedicated server hosting provides customizable security configurations, including firewall protection, intrusion detection systems, and regular security audits, bolstering defense mechanisms against malicious activities and unauthorized access. The power of dedicated server hosting in India for high-traffic websites lies in their unmatched performance, scalability, reliability, and security. As the digital landscape continues to evolve and user expectations soar, dedicated server hosting remains the cornerstone of robust online presence. By investing in dedicated server hosting, website owners can ensure optimal performance, scalability, and security, laying a solid foundation for success in the digital age.
Gatekeepers of Tomorrow – Access Control in the Digital Age
In the ever-evolving landscape of the digital age, access control has emerged as the gatekeeper of tomorrow, reshaping the way we navigate and secure our virtual realms. As our lives become increasingly intertwined with technology, from smart homes to cloud-based services, the need for robust access control mechanisms has never been more crucial. Access control, at its core, is the practice of regulating who can access or use resources in a given environment. In the digital realm, this encompasses a wide range of entities, from individuals accessing personal data to organizations safeguarding critical information. The traditional paradigm of access control, often revolving around passwords and authentication codes, is being augmented by cutting-edge technologies such as biometrics, multifactor authentication, and artificial intelligence. Biometrics, with its ability to authenticate based on unique physical or behavioral traits, is at the forefront of the access control revolution. Fingerprints, facial recognition, and even voice patterns are becoming the keys to our digital kingdom. This shift not only enhances security but also streamlines user experience, eliminating the need to remember complex passwords.

Multifactor authentication takes this a step further by combining multiple forms of identification, adding an extra layer of defense against unauthorized access. The dynamic nature of access control is exemplified by adaptive authentication, where the system continuously evaluates risk factors and adjusts security measures accordingly. This adaptability is crucial in an era where cyber threats are constantly evolving. Artificial intelligence, with its ability to analyze vast amounts of data in real-time, plays a pivotal role in fortifying access control. Machine learning algorithms can detect anomalies in user behavior, identifying potential security breaches before they escalate. Predictive analytics enable proactive measures, anticipating and mitigating risks before they materialize. Moreover, AI-driven systems can learn from patterns and trends, constantly refining their ability to distinguish between legitimate and malicious activities. This self-improving aspect of AI aligns seamlessly with the dynamic challenges of the digital age.
Instead of relying solely on firewalls and other perimeter security measures, Zero Trust assumes that threats may exist within the network. Every user, device, and application is treated as potentially untrusted, requiring continuous verification. Approach san antonio access control system, coupled with advanced access control technologies, ensures a more resilient defense against sophisticated cyber threats. However, as access control evolves, ethical considerations and privacy concerns loom large. Striking a balance between security and individual privacy becomes paramount. As access control mechanisms become more sophisticated, there is a growing need for transparent policies, informed consent, and robust legal frameworks to safeguard user rights. In conclusion, access control in the digital age is a multifaceted endeavor, weaving together technological innovation, artificial intelligence, and ethical considerations. As the gatekeepers of tomorrow, these systems not only protect our digital assets but also redefine the boundaries between security and privacy in an interconnected world. The future promises even more advancements, challenging us to navigate the delicate balance between security imperatives and individual freedoms.


